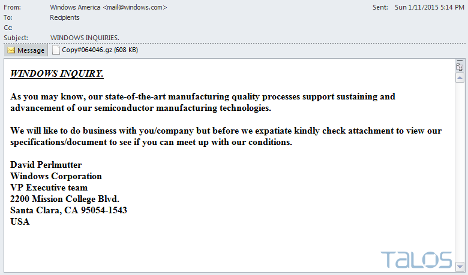
During social engineering exercises, one of the difficulties we face is to get a person to click a link or open an attachment. For the past few decades, we haven’t seen much changes in it. A rather, *sad* part even, a few days ago; Cisco researchers wrote about a quite aggressive malware; Rombertik. While being relatively technically advanced (uncalled functions, anti debugging techniques, etc), one of the modes of distribution is through phishing emails, and quite bad one at that:
A better way is to do targeted attacks; i.e: spear phishing attacks, where you focus your attack on a few people, rather than just casting a net and seeing what sticks.
For this, during social engineering engagements, we often like to use the following 2 techniques:
- Fake CC
- Fake email thread
Fake CC
Emails have the power to be sent to multiple people, but unlike its analog paper letter cousin, if that mail is sent to you, you can see who was in the “To” and who is in the “CC” field; you can’t see BCC’s, obviously (although, if your address isn’t in the TO or CC fields, you were probably BCC’d).
An email’s CC is just a MIME header, it’s nothing more than saying “Hey, I also sent this message to X and Y”. Since these MIME headers are in the email body, they’re interpreted nicely by your email client, not by the SMTP server. The SMTP server takes care of delivery, whatever the content is. Sending an mail saying:
From: mike@flurk.org
To: your@address.com
CC: obama@whitehouse.gov
Subject: Let’s all meet upHey guys, why don’t we ll meet up this weekend?
Would show in your email client that Obama was CC’d, but unless there was an SMTP instruction (RCPT TO: obama@whitehouse.gov), it didn’t really happen. With this, we try to trick our social engineering targets to believe that we also emailed their colleagues, bosses, etc. It’s a sort of collective guilt sharing; “Well, I don’t really trust this. But since it was CC’d to my team, it is probably true/legit”.
Of course, it looks odd when we’re sent an email without any preface to it, which brings us to:
Fake Email Thread
Since we all witnessed it, we all “trust” email threads. Person A and B and emailing back and forward, and eventually include you; directing and action. A potential social engineering scenario could go in these lines:
– Boss: Our VPN is slow.
– Colleague: There’s an update for the VPN client software, it’s much faster. I’ll have IT come and install it.
– Boss: It is faster indeed, let’s push it out to the team.
– Colleague: Dear all, as directed by the boss, please upgrade your VPN client with http://evil.com/client.exe
You check the “email history”, and see how the software was tested, and approved by people you supposedly trust; increasing the chance of you installing the software.
I spoke about this a few months ago in HelpAG’s Spotlight event (slides), so I thought I’ll put it here too. In the end, we shouldn’t just trust what is emailed to us.
Leave a Reply