 TL,DR; download the script here.
TL,DR; download the script here.
In security audits, when we get a password file we -even though we may have admin or root access on the target already- usually grab the password file for offline cracking, just to see if there’s any passwords that users re-use, which would give us more access to other systems.
Doing so, we sometimes find passwords such as “cft6&YGVbhu8“, which by the looks of it seem secure; they have uppercase characters, special characters and numbers. When typing them, you’ll notice that they are keyboard patterns.
For this, I was wondering if it was possible to generate a list of all/many keyboard pattern based passwords, a technique referred to as “key walking“. Some tools exist already, but are often based on predefined patterns (“qwe”, “asdf”, “1qaz”, …). I wanted to make something based on a keyboard layout, so it could be extended. This is KeyWalker; a ruby script that generates keyboard pattern based passwords.
Currently, the KeyWalker script performs the following patterns:
- Parallel Sequences: This mode provides a series of parallel sequences in the same direction. This generates passwords such as “345etrdfg”.
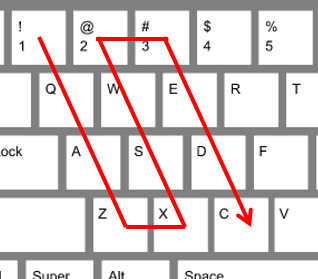
- ZigZag: Like “1qazxsw2”, this mode provides a “back and forth” sequence on a keyboard while shifting rows / columns.
- Circle: Generates a shaped, half/full circle sequence of keys. This generates string such as “1234rfvcxz”
The code is available on GitHub, but is obviously a work in progress. Feel free to fork the code and make any additions. Also, the file with the generated passwords is there too.
Extra:
Some online URL’s password complexity checkers (such as nisc, passwordmeter or HowSecureIsMyPassword) check for keyboard patterns, but only detect basic sequential ones and shows that a password like “1qazXSW@3edc” is seen as “secure”, whereby it’s just a pattern.
Leave a Reply